Tecton’s Security & Compliance Journey to SOC 2 Type 2

Tecton is SOC 2 Type 2 compliant (but that’s not what this post is about)
If you search for “SOC 2 Type 2 announcement” you’ll find troves of blog posts from companies of all sizes, so that’s not what this blog post is about. Instead, I am going to walk through Tecton’s journey of gaining customer and user trust from the early days to now along with a firsthand account of navigating SOC 2 as an early employee in a fast-growing startup.
If you’re only interested in learning about our SOC 2 Type 2 designation, here it is:
Today we’re proud to announce that Tecton has received its SOC 2 Type 2 report! This designation is a testament to nearly 2 years of effort implementing, operating, maintaining, and monitoring a comprehensive set of internal controls and practices across Tecton’s organization and infrastructure. The report is the final step of a months-long audit process performed by a licensed and independent CPA audit firm. Most importantly, the report was issued with zero exceptions! (more on this below)
Early days
After 6 years at Google, I took the leap into startups and joined Tecton as a software engineer. At the time, Tecton was in stealth mode (the website was literally a picture of a mountain) with a team consisting of the founders and 2 other engineers. People in tech love the classic tale of joining a startup, moving fast and breaking things (but that’s okay because you’re at a startup), and pushing to production like the world depends on it. To some extent, this was the state of the world at Tecton back then — we had early customer traction, a product that was rough around the edges, and not-so tried and tested infrastructure.
The “break things” model might work for a Consumer product, but this model won’t last very long in an Enterprise SaaS product. Tecton solves the data challenges around ML, which is the hardest part of deploying ML into production — customers need to trust Tecton with their data. Tecton’s first few employees came from companies like Google, Uber, and Facebook, so we knew a thing or two about how big companies securely operate. For example:
- Onboarding new hires? They’re not going near anything mission-critical until they take extensive training.
- Landing code without a code review? Don’t do it! However, if you must in case of emergency, it’s audited and it’ll need to be retroactively reviewed.
- Someone in marketing with access to production systems? Good luck. That will set off some alarms.
By the time I joined Google, it was already a mature company and these processes seemed pretty cumbersome, but they were the norm so no one questioned them. The need for such processes started making a lot more sense once I left Google to help build Tecton. Our Feature Store has been built with security in mind from the ground up, but it’s important to understand that security responsibilities span beyond just Engineering. Security and compliance isn’t the job of an individual or team — it’s an organization-wide process transformation.
As an early engineer, I was invited to many sales meetings to walk through technical requirements. I distinctly remember one prospect asking us “You must have 100+ employees, right? How big is your security team?” Little did they know, half of Tecton’s employees were sitting in the room with them.
Security and compliance requests start flowing in
Many of our prospective customers asked us to fill out lengthy vendor security questionnaires with 100s of questions. Every questionnaire had completely different formatting, but the content was always more or less the same. We began looking for alternatives to filling out these seemingly never-ending forms on a weekly basis and, eventually, some customers started asking about security designations.
It quickly became clear that we needed to pursue SOC 2 Type 1 and 2, which are table stakes for any Enterprise SaaS company. This led to our first security and compliance hire roughly one year after Tecton was started. Having a dedicated expert was a crucial step in our success with SOC 2 compliance as well as for Tecton’s overall maturity — most startup founding teams don’t include a security expert so hiring one is a critical step in the organization’s maturity.
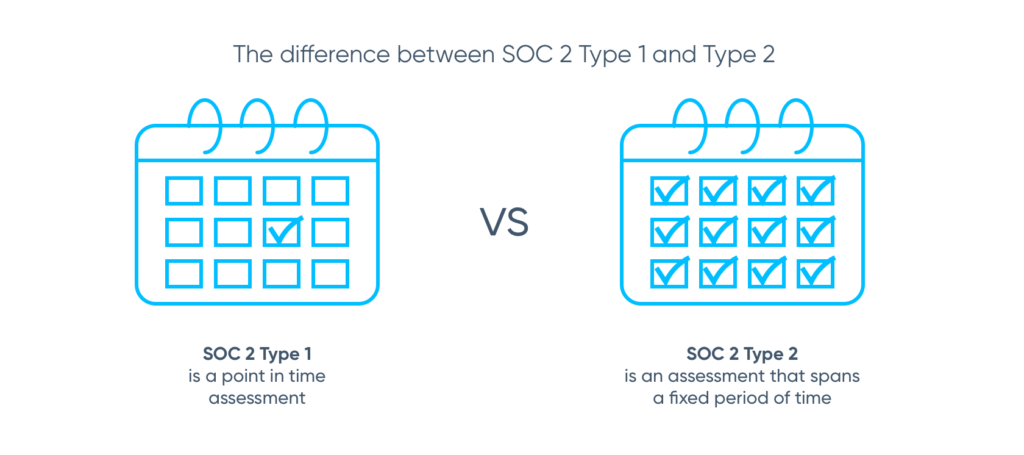
SOC 2 Type 1 and 2 reports are based on an external audit based on the American Institute of Certified Public Accountants (AICPA) Statement on Standards for Attestation Engagements (SSAE 18). The difference, in a nutshell, is:
- SOC 2 Type 1 is a point in time assessment, in which the external auditor attests Tecton has indeed implemented and laid the groundwork for the controls required by SOC 2. Tecton received its Type 1 designation in September 2020.
- SOC 2 Type 2 is an assessment that spans a fixed period of time (usually 6 months or a year) where the external auditor attests Tecton’s controls have operated effectively for the entire evaluation period. Tecton received its Type 2 designation in October 2021.
SOC 2 Type 1: Lay the foundation
The process started by hiring an audit firm and having a series of lengthy sessions with our security, compliance, and engineering team about Tecton’s current internal processes (a.k.a. “controls”) to identify any that need to be hardened or implemented to meet the rigorous standards of SOC 2.
Fast-forward many months, Tecton underwent its SOC 2 Type 1 audit and our SOC 2 Type 1 report was officially issued in September 2020.
Don’t be the bad guy!
The goal of SOC 2 is to implement robust processes that make it easy for people to do the right thing and nearly impossible to do the wrong thing. There are tools like Vanta that can help automate this, but any approach will require buy-in from the entire company including Engineering, Product, Sales, Customer Success, HR, and Legal. If you feel like the bad guy chasing everyone down to do the right thing, you are doing the wrong thing. It’s important to approach compliance proactively with a systems approach rather than a reactive approach.
SOC 2 Type 2: Put your money where your mouth is
In plain English, SOC 2 Type 1 is “congrats, you have demonstrated design and implementation of the necessary controls“. Type 2 is “now prove that you’re actually following the rules you implemented“. Tecton’s sales flywheel was spinning fast by the time the Type 1 report was issued, so it was no surprise that I started getting questions about Type 2 almost immediately.
Zero Exceptions!
An audit exception on a SOC 2 report is an instance where controls are not designed or implemented appropriately or it did not operate as intended (i.e. the rules were broken!).
As a testament to Tecton’s organization-wide transformation and adoption of security and compliance, we are proud to announce its SOC 2 Type 2 report had zero exceptions.
Looking forward
Tecton is, at its core, the same company it was when I joined over 2 years ago. We’re a team of experts with a bias to action and moving fast and, of course, we still break the occasional thing (any SaaS company that claims they don’t break anything isn’t telling truth).
A lot has changed though: Tecton’s employee count has multiplied more than 6 times since the beginning of our SOC 2 journey and we have customers who trust us with high volume business-critical data. The team now has dedicated DevOps and Security experts, a fantastic People and HR team, along with several other growing teams within the company.
SOC 2 Type 2 is a never-ending journey so Tecton will continue to improve its practices and perform audits in perpetuity to refresh the designation. Beyond SOC 2, Tecton plans on pursuing many of the other designations that are common for trusted Enterprise SaaS software companies.
For more information about Tecton’s security profile, check out our whitepaper at https://www.tecton.ai/security/.
